Users
Security & Compliance Teams, Payment Systems, Engineering Teams
Industry
Financial Services / Payments
Product Stage
Mature, Security-Critical Platform
Encryption Platform for Card Payments
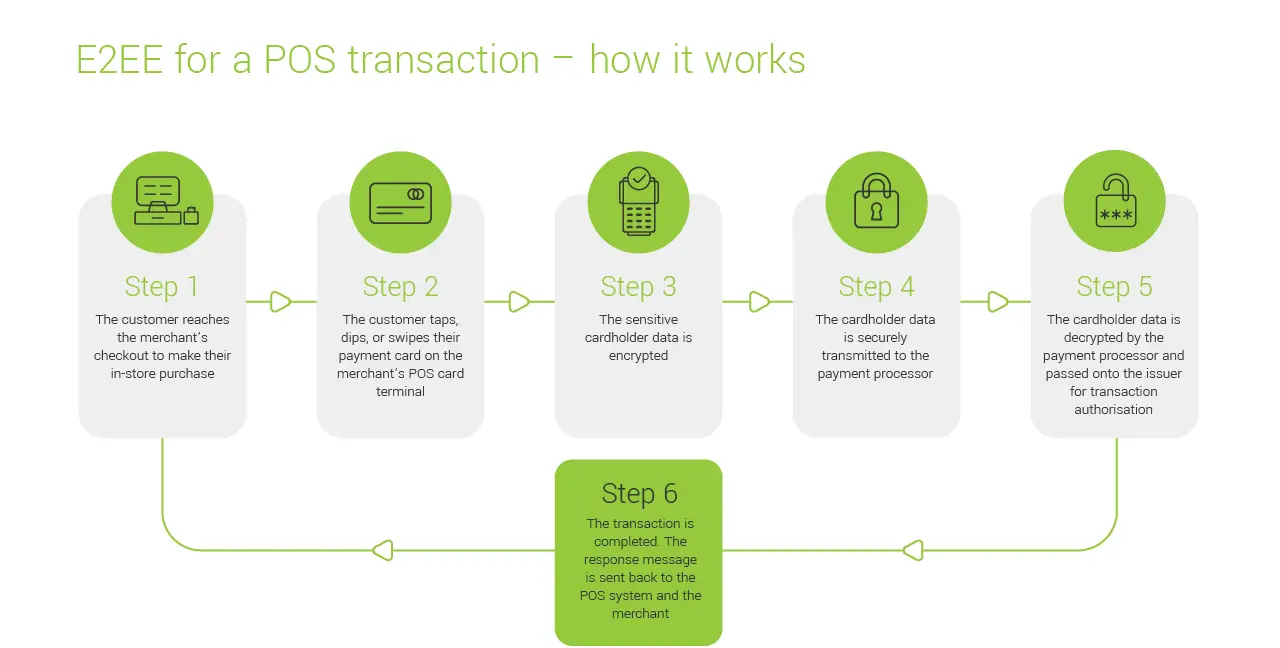
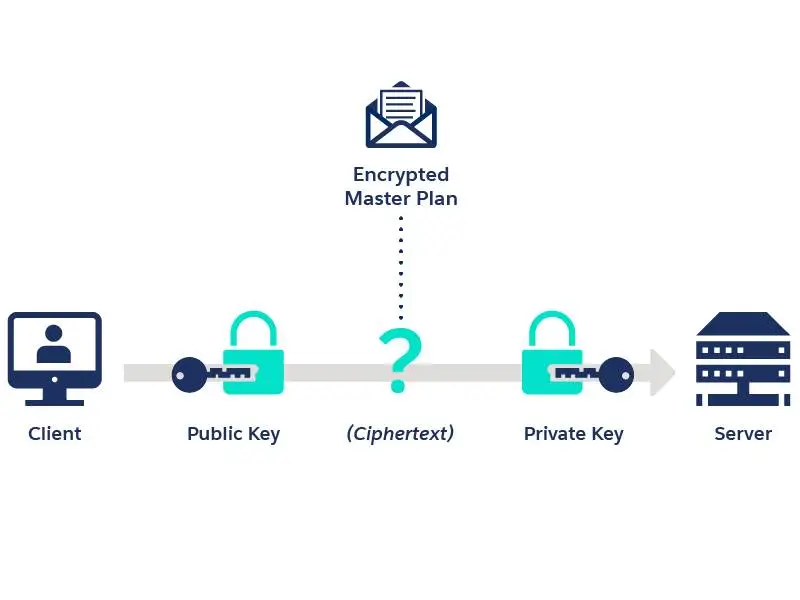
The encryption platform sat underneath every card payment flow, responsible for protecting sensitive cardholder data as it moved across internal systems and external networks. Unlike visible product surfaces, this platform only drew attention when something went wrong like a security gap, a compliance concern, or friction introduced into payment processing.
At the same time, it had to operate invisibly: strong cryptography, strict key management, and regulatory alignment, all without slowing down real-time payment flows or disrupting dependent systems.
Context and Scale
This platform supported card payment processing at global scale:
-
Encrypting and decrypting sensitive payment data across multiple transaction paths
-
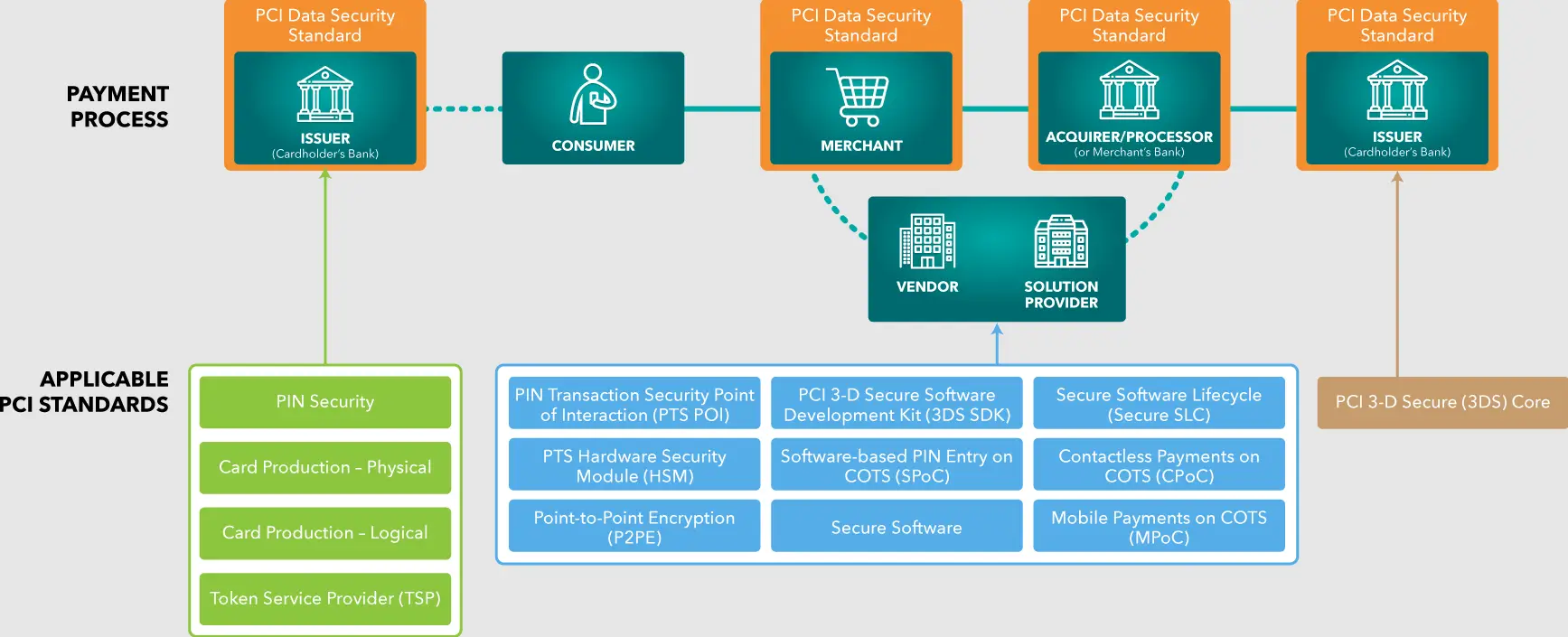
Operating under strict regulatory and compliance requirements
-
Serving engineering, security, compliance, and operations teams rather than end users
Encryption decisions directly affected:
-
Data security and breach risk
-
Compliance posture and audit outcomes
-
System performance and operational complexity
Once in place, encryption mechanisms are hard to change which made early decisions especially high-stakes.
The Problem
As payment flows evolved, the existing encryption approach began to show strain.
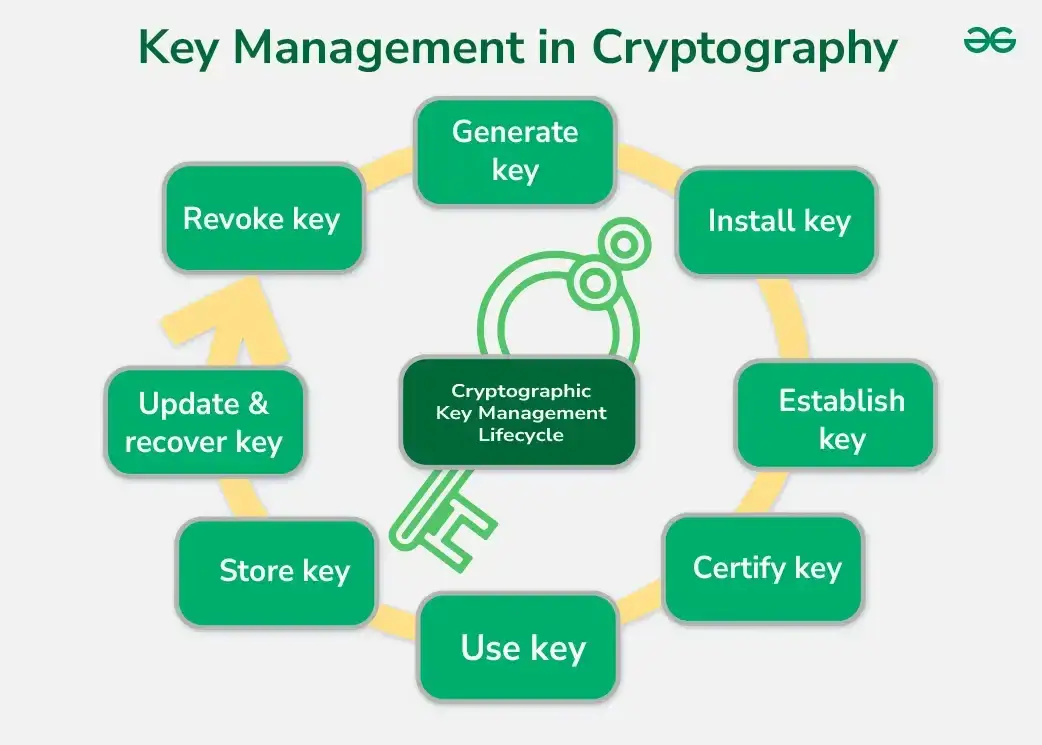
New payment methods and integrations increased the number of systems handling sensitive data. Compliance expectations around key management, rotation, and auditability became more stringent. At the same time, performance expectations remained unchanged, encryption could not become a bottleneck in real-time processing.
The challenge was to strengthen security guarantees and compliance alignment without:
-
Increasing latency in payment flows
-
Introducing brittle dependencies between systems
-
Making the platform harder to operate or evolve
My Role
I was responsible for how encryption capabilities evolved across the payments platform.
That included:
-
Defining the product direction for encryption and key management capabilities
-
Prioritizing security and compliance requirements against platform complexity
-
Aligning engineering, security, and compliance teams on what “good” looked like before changes were introduced
Much of the work involved translating security and regulatory requirements into product decisions that were operable at scale.
Decisions
Several decisions had long-term impact:
One was where encryption boundaries should live. Rather than spreading cryptographic responsibility across many services, encryption responsibilities were consolidated to reduce duplication and inconsistency. This simplified audits and reduced the risk of uneven security posture across systems.
Another was how key management and rotation were handled. The focus was on mechanisms that were secure by default and auditable, but also predictable to operate, avoiding solutions that met compliance on paper but created operational fragility.
There were also tradeoffs around security depth versus integration friction. In some cases, tighter controls would have slowed down adoption or complicated integrations. Decisions favored approaches that raised the baseline security posture while keeping the platform usable for teams building on top of it.
Risks
Poor decisions in this space carried serious consequences:
-
Increased exposure of sensitive cardholder data
-
Compliance failures and audit findings
-
Operational instability caused by overly rigid security mechanisms
Managing these risks meant being conservative about change, explicit about assumptions, and deliberate about rollout paths.
Outcomes
The platform strengthened its security posture without becoming a bottleneck for payment processing. Encryption and key management behavior became more consistent and easier to reason about across systems. Compliance conversations shifted from reactive remediation to confidence in how sensitive data was handled.
Just as importantly, downstream teams were able to build and evolve payment capabilities without repeatedly re-solving encryption concerns.