Users
End Users, Enterprise Customers, Security & Compliance Teams, Product & Engineering Teams
Industry
Cybersecurity / Enterprise SaaS
Product Stage
Mature, Privacy-Critical Platform Capability
Consent Management & Data Privacy Controls
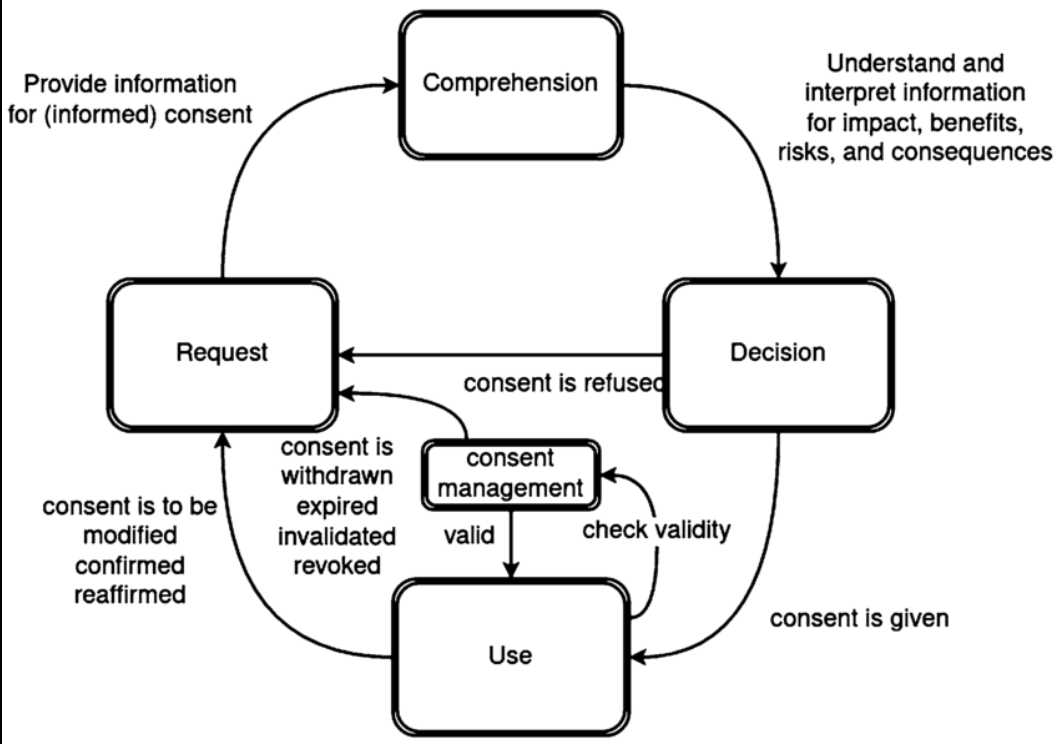
Consent management was where data privacy strategy became real. Unlike regulatory planning or audit readiness, consent lived inside active user journeys and system workflows, where correctness mattered at runtime, not just on paper.
The challenge wasn’t collecting consent once, it was ensuring that consent states were accurately captured, propagated, enforced, and respected across systems as users, products, and policies evolved.
Context and Scope
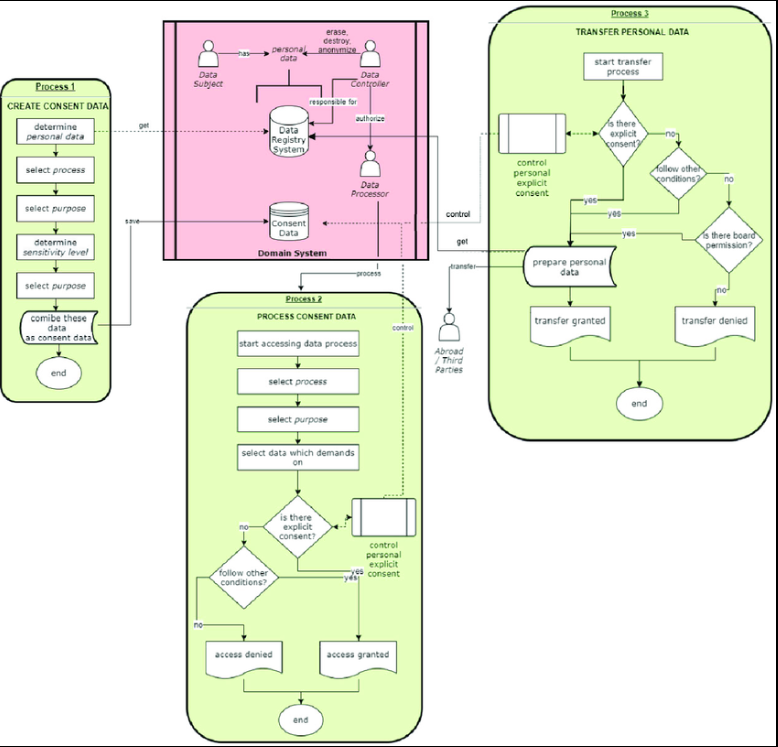
The platform handled sensitive identity and customer data across multiple products and services. Users interacted with the system through account creation, purchases, renewals, and ongoing product usage, each of which could introduce new consent requirements or modify existing ones.
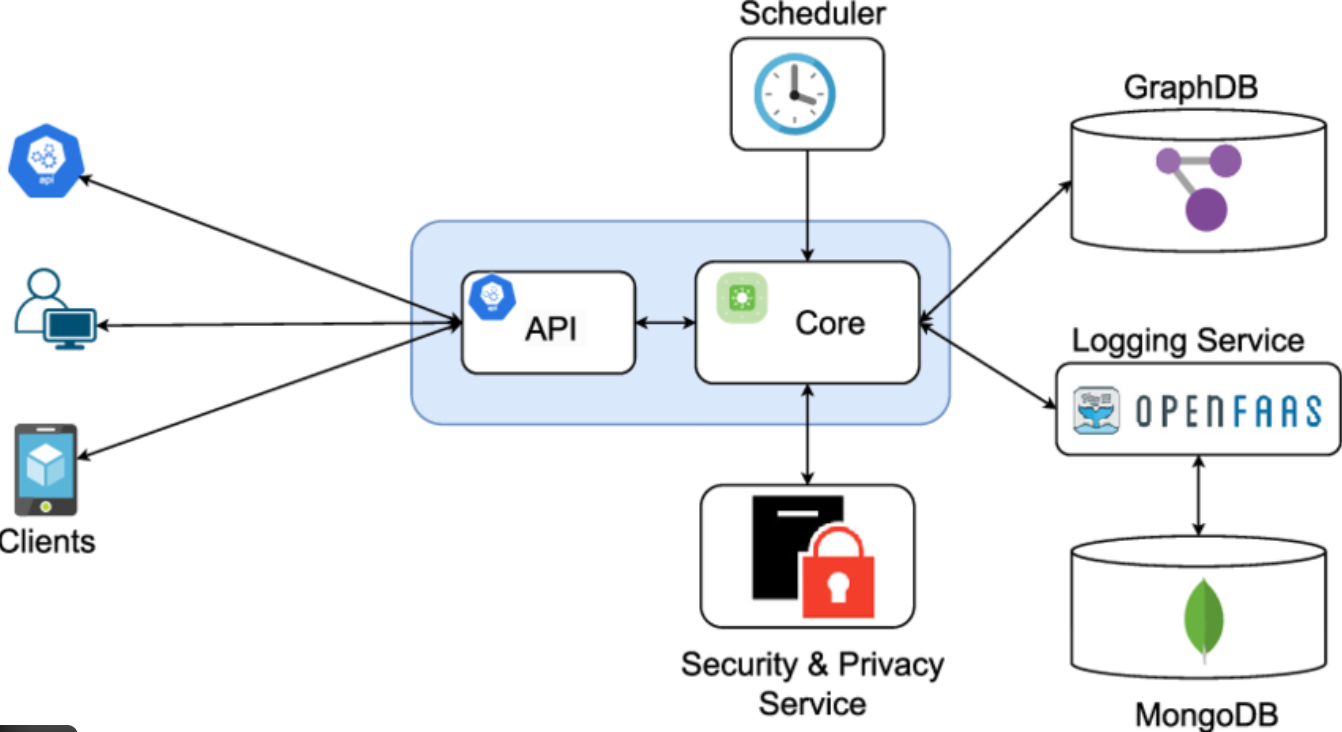
Consent decisions needed to be durable, traceable, and enforceable across distributed systems. A single inconsistency where one system honored consent and another didn’t, could create regulatory exposure and undermine customer trust.
This made consent management a foundational runtime capability, not a compliance afterthought.
The Problem
Consent was fragmented across products and workflows.
Some systems captured consent implicitly, others explicitly, and enforcement varied depending on where data was accessed or processed. Changes to consent such as revocation or scope updates were not consistently propagated, creating ambiguity around what data could be used, by whom, and for what purpose.
The core problem was designing a consent model that was both human understandable and machine enforceable, without slowing down product delivery or overcomplicating user experiences.
My Role
I was responsible for defining consent management as a product capability, not just a UI interaction or legal artifact.
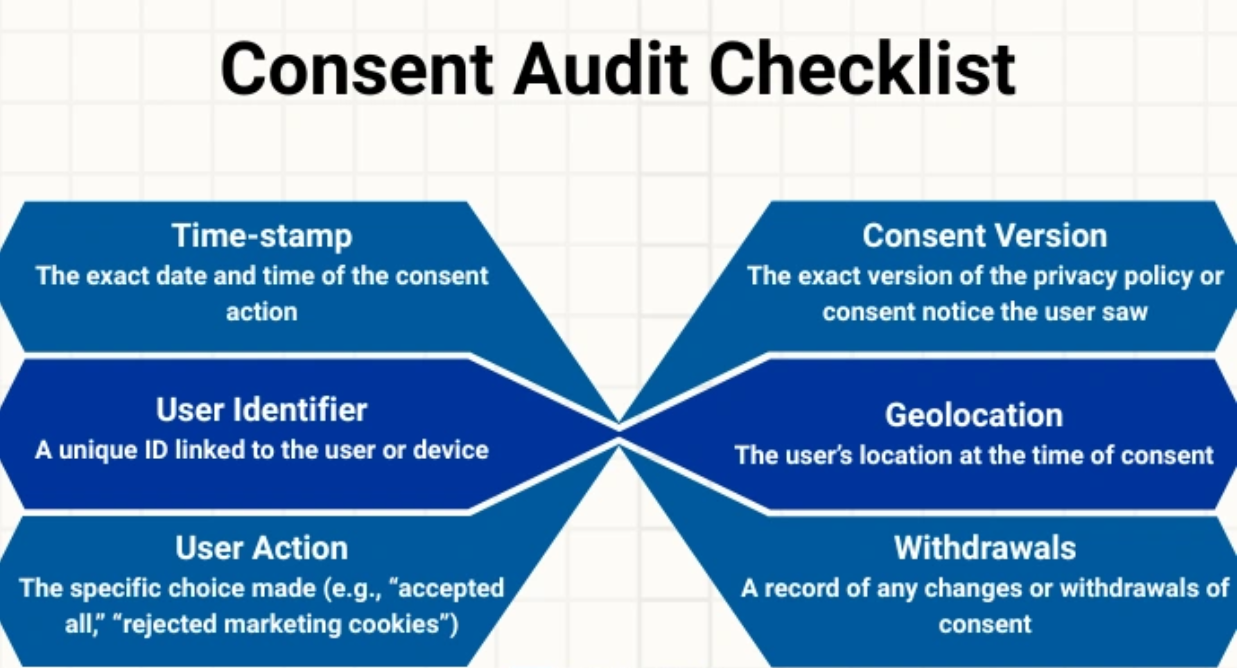
That meant shaping how consent was captured, versioned, and stored, and how consent states were evaluated at runtime when systems attempted to access or process personal data. I worked closely with engineering, security, and legal stakeholders to align on consent semantics that were precise enough for enforcement while remaining clear to users.
A key part of the role involved resolving ambiguity translating policy language into deterministic product behavior that systems could rely on without interpretation.
Decisions
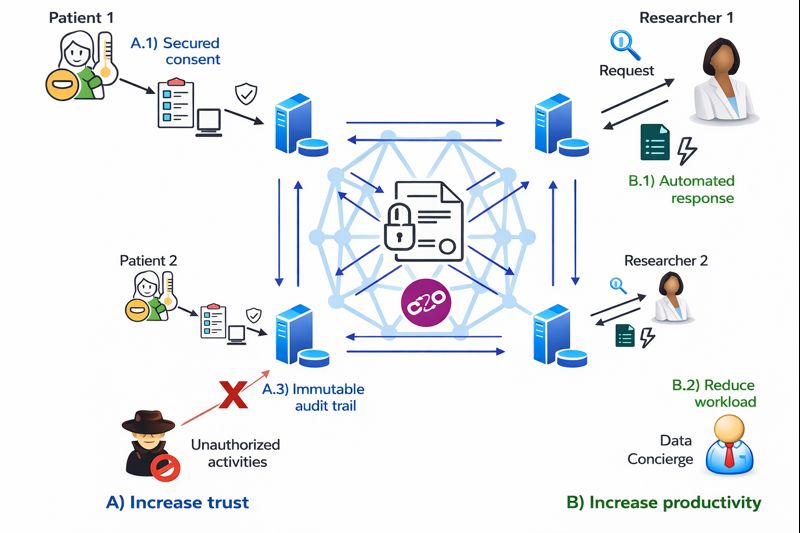
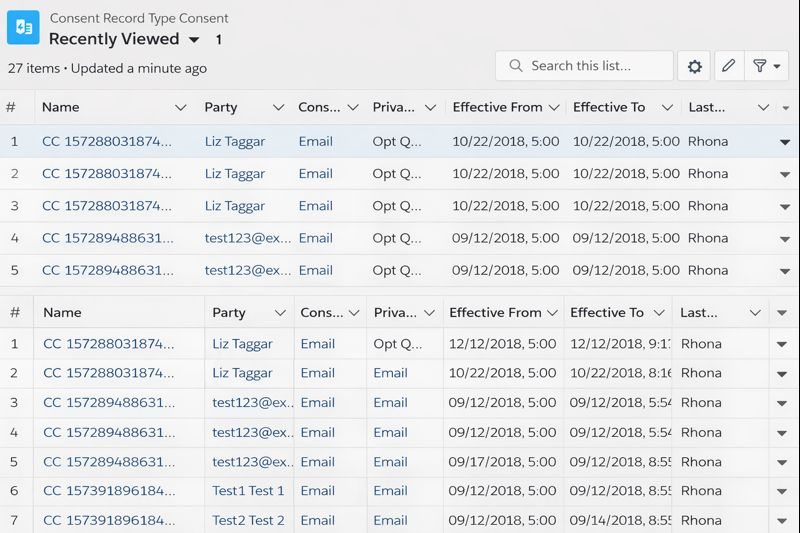
One key decision was to centralize consent state rather than allowing each product to manage it independently. This created a single source of truth that reduced inconsistency and made enforcement predictable.
Another was explicitly modeling consent scope and purpose, rather than treating consent as a binary flag. This allowed the platform to support differentiated use cases while still enforcing boundaries when consent changed or was withdrawn.
There were also deliberate decisions around change handling. Consent updates were treated as events with downstream impact, ensuring that revocation or modification triggered appropriate restrictions across affected systems.
Risks
Consent failures are subtle but severe.
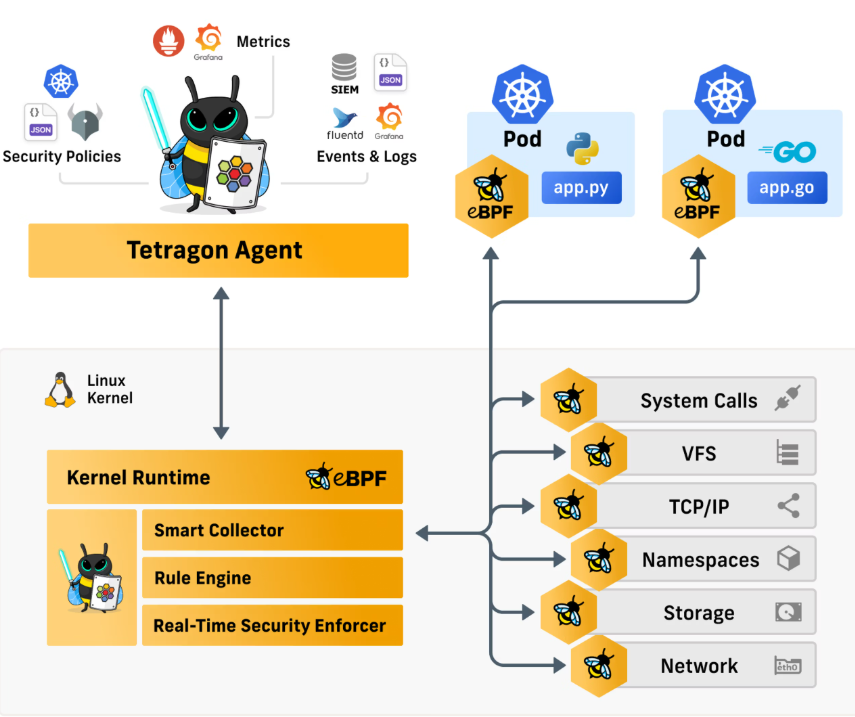
Over-enforcement can break legitimate product functionality. Under-enforcement can violate user expectations and regulatory requirements. Poor visibility into consent state can slow incident response and undermine audits.
Managing these risks required tight alignment between product intent, system behavior, and operational monitoring and resisting shortcuts that treated consent as static or incidental.
Go-To-Market
The go-to-market approach positioned consent management as a trust and control capability, embedded into core product workflows rather than surfaced as a standalone feature.
For customers, consent controls reinforced transparency and confidence in how data was handled. For enterprise buyers and security reviewers, the presence of explicit, enforceable consent mechanisms reduced friction during privacy assessments and procurement reviews.
Internally, consent management became a prerequisite for launching new data driven features, ensuring that privacy considerations scaled alongside product innovation rather than lagging behind it.
Outcomes
Consent handling became more consistent, auditable, and enforceable across the platform. User preferences were respected reliably, and downstream systems operated with clearer guarantees about what data they could access and why.
Most importantly, consent shifted from being a compliance risk to a productized control, enabling safer iteration and greater customer trust.