Users
Enterprise Security Teams, Platform Engineering, DevOps & Operations Teams
Industry
Cybersecurity / Enterprise SaaS
Product Stage
Mature, Trust-Critical Platform Capability
Identity & Certificate Lifecycle Integration
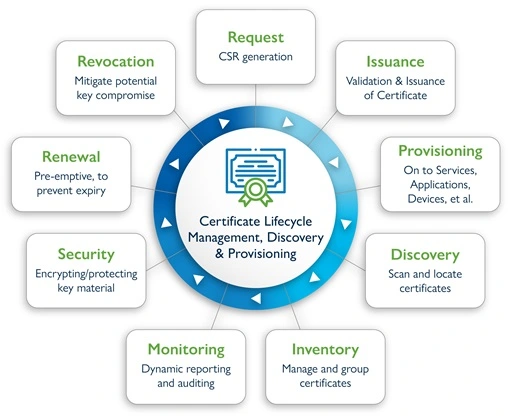
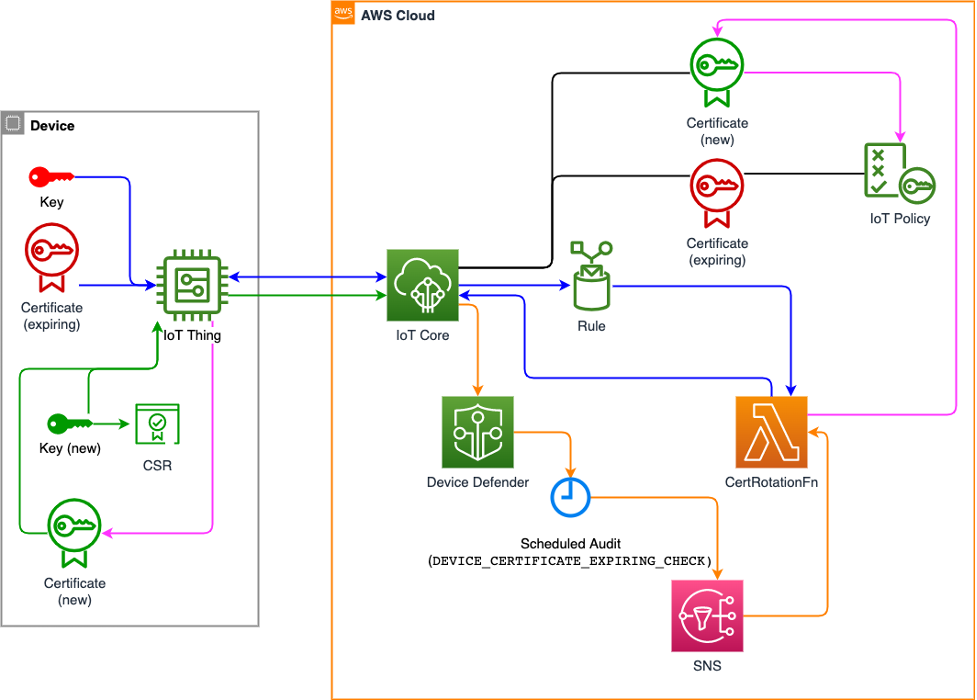
Identity and certificate lifecycle management sat at the foundation of platform trust. Certificates were not static artifacts, they were living entities that needed to be issued, rotated, revoked, and audited in alignment with identity, policy, and operational reality.
As the product ecosystem expanded, certificates touched more systems, more users, and more automated workflows. Without a cohesive lifecycle strategy, identity drift, expired certificates, and inconsistent controls became operational and security risks rather than edge cases.
Context and Scope
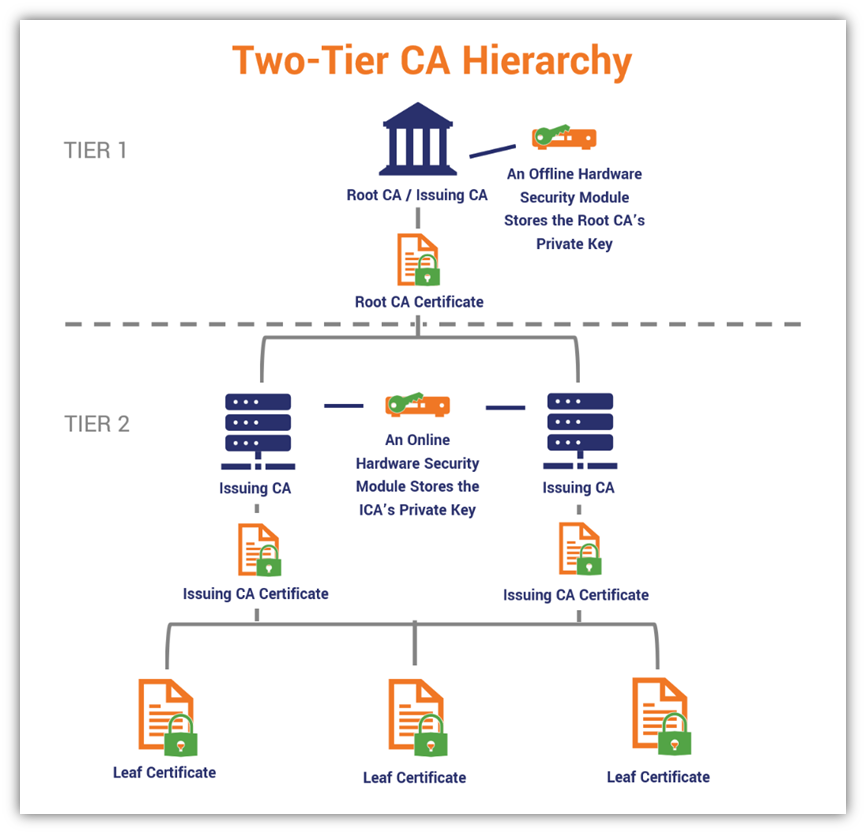
The platform supported certificate issuance and management across a range of use cases, including enterprise systems, applications, and automated services.
Certificates were tied to identities that evolved over time. Users changed roles, services scaled dynamically, and environments became more ephemeral. Managing certificates in isolation from identity context made it difficult to enforce consistent policies or reason about trust relationships.
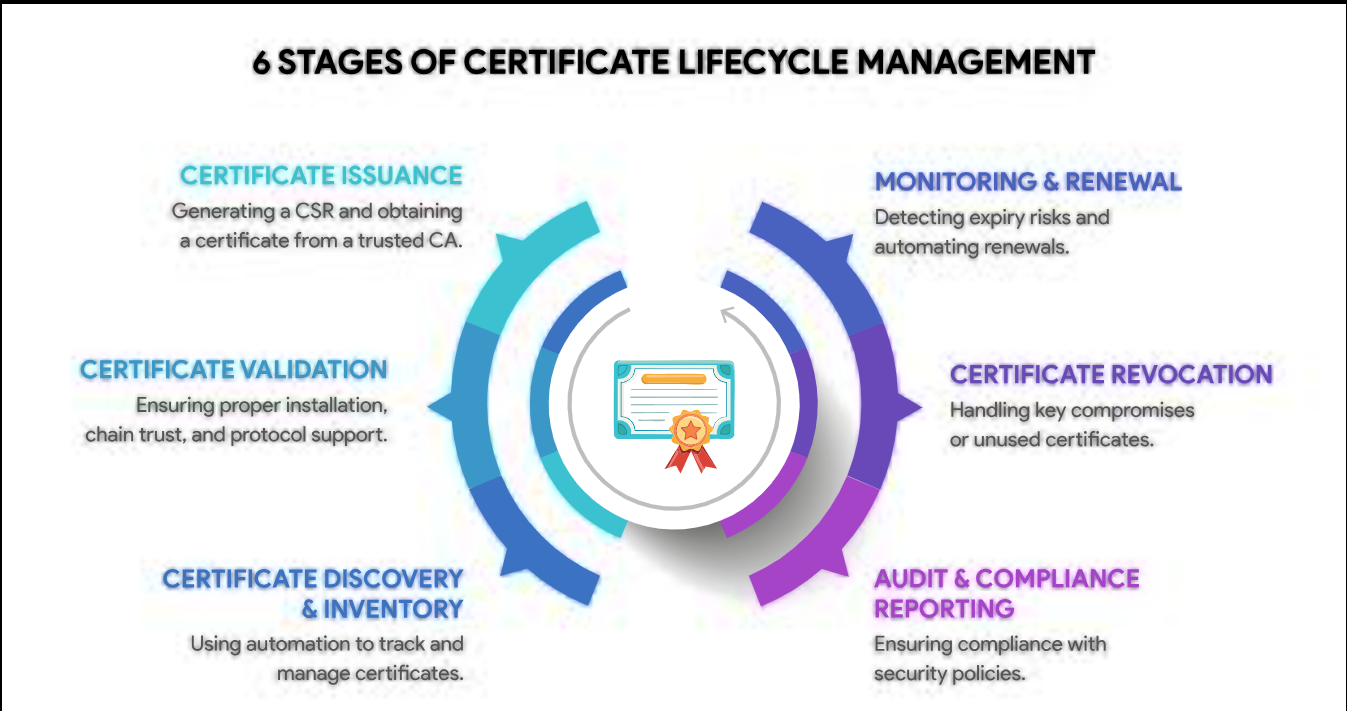
At scale, certificate failures were highly visible. Expirations caused outages, misconfigurations weakened security posture, and lack of visibility made remediation reactive instead of preventative.
The Problem
Certificate lifecycle workflows were fragmented.
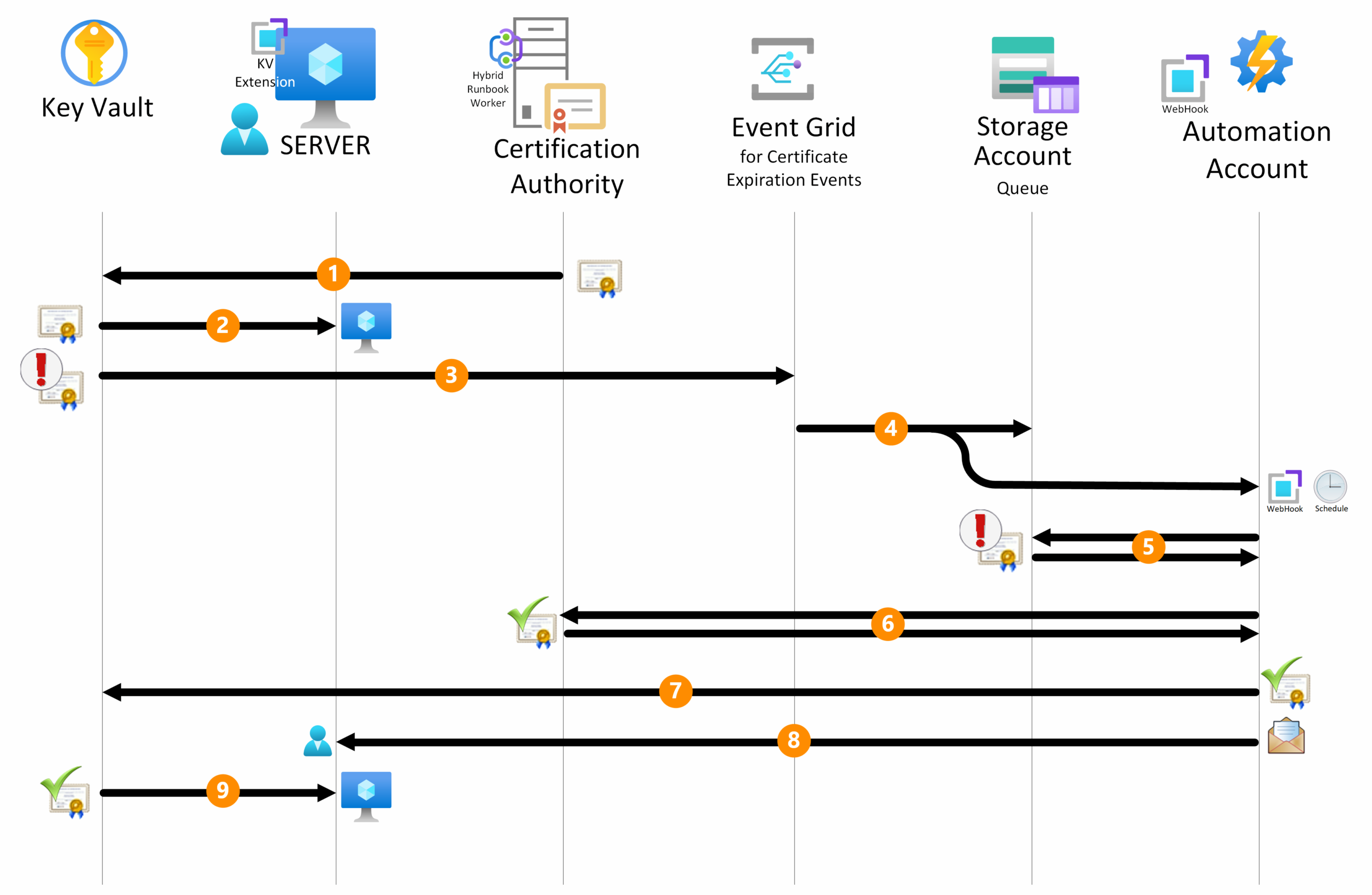
Issuance, renewal, and revocation often relied on separate systems and manual coordination. Identity data was not always consistently linked to certificates, making it harder to understand ownership, intent, or blast radius when issues occurred.
The core problem was integrating identity and certificate lifecycles in a way that supported automation, policy enforcement, and visibility without increasing operational complexity for teams already managing critical infrastructure.
My Role
I was responsible for defining how identity and certificate lifecycles intersected as a product capability, not just a security function.
That meant working across product, security, and engineering teams to define ownership models, lifecycle states, and integration points that aligned identity context with certificate behavior. I focused on ensuring that certificates could be issued, rotated, and revoked in ways that reflected real-world identity changes and operational needs.
A key part of the role involved balancing automation with control enabling lifecycle automation where possible while preserving clear governance and auditability for enterprise environments.
Decisions
One important decision was to treat certificate lifecycle events as first class product signals rather than background processes. Issuance, renewal, and revocation were surfaced in ways that allowed teams to understand and act on changes proactively.
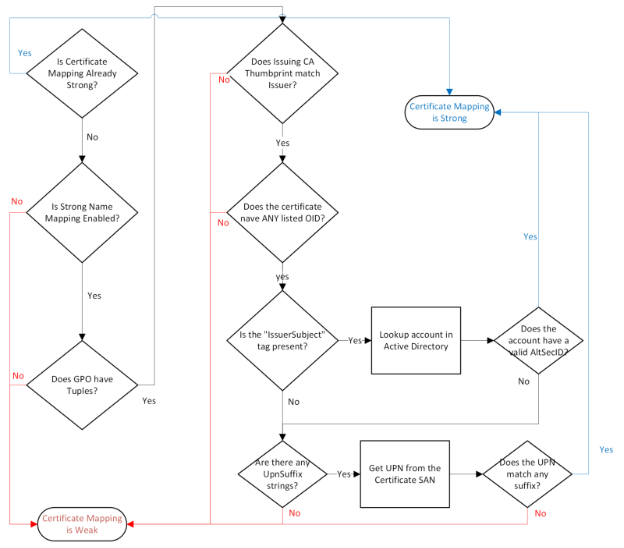
Another was defining clear boundaries between identity sources and certificate management logic. Rather than tightly coupling systems, integrations were designed around stable contracts that allowed identity systems to evolve without breaking certificate workflows.
There were also deliberate tradeoffs around policy flexibility. The platform supported different identity-driven policies without becoming overly permissive, ensuring consistent enforcement while accommodating varied enterprise requirements.
Risks
Lifecycle integrations fail in subtle but dangerous ways.
Missed renewals can cause outages. Overly aggressive revocation can disrupt services. Poor identity linkage can make incident response slower and less precise.
Managing these risks required explicit lifecycle modeling, careful sequencing of automation, and continuous alignment between product, security, and operations teams.
Go-To-Market
The go-to-market strategy positioned identity and certificate lifecycle integration as a reliability and risk reduction capability, not a standalone security feature.
Rather than leading with technical detail, the product was positioned around outcomes that mattered to enterprise customers: fewer outages due to expired certificates, clearer ownership of trust relationships, and reduced manual effort in managing certificate operations.
Adoption was driven by integrating lifecycle capabilities into existing certificate workflows, making them the default path rather than optional add-ons. As customers experienced improved stability and visibility, lifecycle integration became a foundational expectation rather than a differentiated feature.
Outcomes
Certificate lifecycle management became more predictable and aligned with identity context. Automation reduced the frequency of expiration-related incidents, while clearer ownership models improved response time when issues occurred.
The platform was better positioned to support modern, dynamic environments where identities and infrastructure changed frequently without sacrificing trust or control.